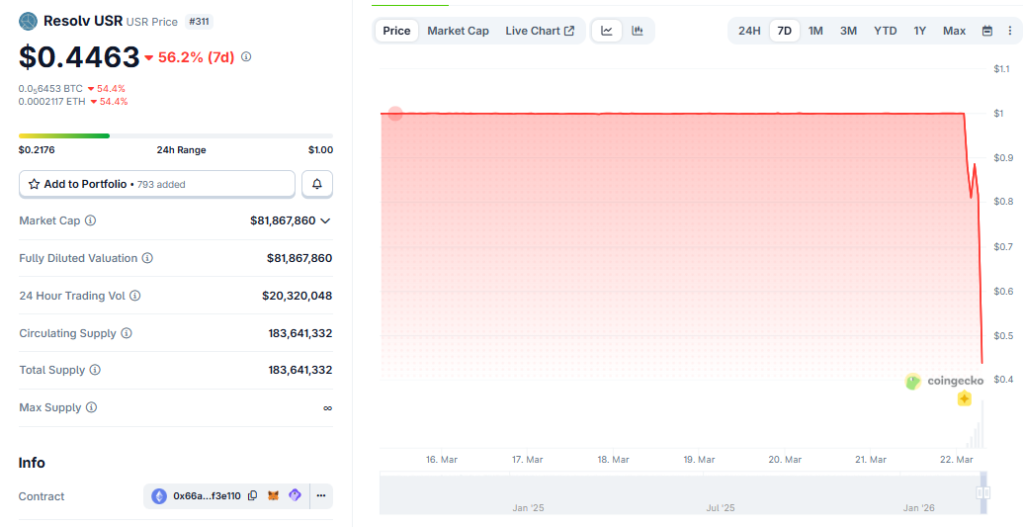
Picture this: a stablecoin designed to stay rock-solid at $1 suddenly plunges to pennies on the dollar. All because one clever hacker turned a tiny $100,000 deposit into $50 million of fake tokens overnight. That’s exactly what happened to Resolv Protocol on March 22, 2026. The entire system ground to a halt, leaving users stunned and the crypto world buzzing with questions.
This wasn’t some massive heist with millions in stolen funds upfront. It was a smart contract glitch that let unbacked tokens flood the market, crashing confidence in seconds. Here’s the full story—broken down in plain English so anyone can understand what went wrong and what it means for you.

Resolv Labs $80M USR Exploit Forces Protocol Pause | Our Crypto Talk
What Is Resolv Protocol? The Basics Anyone Can Grasp
Resolv Labs runs a DeFi platform focused on USR, a stablecoin meant to hold steady at $1 while earning extra yield. Think of it as a smarter savings account in crypto: users deposit assets, the system uses clever balancing tricks (called delta-neutral strategies), and everyone supposedly wins with stable value plus returns.
The protocol had built up trust, managing hundreds of millions in user assets. But like many DeFi projects, it relied on complex code to mint new USR tokens only when real collateral backed them. That trust became the weak spot.
How a $100K Deposit Became $50 Million in Fake Tokens
The attack started small but exploded fast. An unknown person deposited roughly $100,000 worth of USDC (a real stablecoin) into Resolv’s minting system.
Normally, the code should check collateral strictly and issue tokens one-for-one. Instead, a bug in the minting function—possibly tied to how swaps or validations worked—let the attacker create 50 million USR tokens instantly. Security experts later spotted a second transaction adding another 30 million, pushing the total closer to 80 million unbacked tokens.
In simple terms: the system thought it was printing money backed by real assets, but the checks failed spectacularly. The hacker didn’t need fancy hacks or stolen keys—just exploited a tiny logic flaw in the code.
The attacker then quickly swapped those fake USR tokens across decentralized exchanges for real USDC, USDT, and eventually Ether (ETH). Reports estimate they walked away with around $25 million in profit before the chaos fully hit.
The Market Meltdown: USR Crashes Hard
Once the flood of fake tokens hit the market, panic set in. USR, which should stay at $1, dropped like a stone—hitting lows around $0.025 on some platforms and trading as low as $0.20–$0.50 elsewhere. It later clawed back toward $0.80–$0.87, but the damage was done. Liquidity dried up, and traders faced massive slippage.
This depeg wasn’t just a number on a screen. It shook confidence in stablecoins everywhere, reminding everyone that “$1 = $1” only works when the code and collateral actually match.
Hacker Attack on Resolv Crashes USR Stablecoin | ForkLog
Resolv’s Immediate Response: Hitting the Emergency Brake
Resolv Labs acted fast. In an official post on X, the team stated: the platform suffered an exploit allowing 50 million unbacked USR to be minted. They immediately paused all protocol functions—a built-in “kill switch” that froze everything to stop more damage.
Key reassurance from the team: the main collateral pool stayed fully intact. No underlying user assets disappeared. The issue was isolated to the USR minting mechanism. Investigations are ongoing, with PeckShield and other firms helping trace the transactions.
Are User Funds Safe? The Current Situation
Right now, the protocol remains frozen. That means roughly $500 million in broader user positions (according to some reports) are temporarily locked while the team works on a fix. The good news? No assets were drained from the core pools—unlike many past hacks where funds vanished forever.
Recovery efforts focus on restoring service safely, possibly with compensation plans or snapshots of user balances before the exploit. As of March 23, 2026, exact timelines aren’t public, but the emphasis is on protecting holders.
Why This Exploit Hits Home for Regular People
You don’t need to be a blockchain expert to feel the impact. Stablecoins are supposed to be the “safe” part of crypto—great for parking money during volatility or earning steady yields. When one breaks, it reminds everyday investors that code can have hidden bugs, and even “trusted” projects carry risks.
This event also spotlights bigger DeFi questions: How often do audits miss critical flaws? What happens when one bad mint spirals into market-wide fear? And most importantly—how can regular users spot warning signs before jumping in?
Five Lessons Every Crypto User Should Take Away
- Never assume “stable” means risk-free. Even pegged coins can break if the code fails.
- Check audit history. Look for recent, reputable reviews—though even audited projects get hit.
- Diversify your holdings. Don’t put everything in one protocol.
- Watch on-chain activity. Tools like PeckShield alerts can flag suspicious mints early.
- Understand the mechanics. If a project promises high yields with complex strategies, ask: “What backs this if things go wrong?”
What’s Next for Resolv and the Wider Crypto Space?
The team is deep in recovery mode, auditing every line of code and coordinating with security experts. Many in the community hope for a swift restart with stronger safeguards—maybe upgraded validation checks or better oracle protections.
In the bigger picture, this exploit adds to a growing list of DeFi incidents in 2026. It pushes developers to prioritize simpler, battle-tested code over flashy features. For users, it’s a wake-up call to stay informed and cautious.
The Resolv story isn’t over yet. As updates roll in, the focus remains on transparency and getting users’ access back safely. In crypto, speed matters—but security matters more. This $50 million glitch just proved it again.






















