Picture this: It’s a quiet Saturday in April 2026, and suddenly one of the biggest liquid restaking protocols in crypto loses nearly $290 million in a single sophisticated strike. No smart contract bug. No flashy code exploit. Just a clever trick that turned a cross-chain bridge into an open vault. That’s exactly what happened to KelpDAO’s rsETH token on April 18. LayerZero, the messaging protocol powering the transfer, quickly stepped forward with a clear message: the breach wasn’t their core system failing—it was a single point of failure in how KelpDAO set up its security checks.
This isn’t just another headline for crypto insiders. With DeFi handling billions in everyday user funds, incidents like this remind regular people why bridge security matters. Here’s a straightforward, no-jargon breakdown of what went wrong, who’s pointing fingers, and what it means going forward.
What Exactly Happened: The $290M KelpDAO Exploit Unpacked
On April 18, 2026, attackers drained roughly 116,500 rsETH—worth about $290 million—from KelpDAO’s cross-chain bridge. rsETH is KelpDAO’s liquid restaking token, designed to let users earn yields while keeping their assets flexible across different blockchains.
The hack didn’t break any core code. Instead, it targeted the infrastructure that verifies messages moving between chains. Hackers compromised specific RPC nodes (the servers that relay blockchain data) used by LayerZero’s verifier system. They then launched a DDoS attack to force the system to rely on their poisoned data. The result? A fake “cross-chain transfer” message was approved, minting unbacked rsETH that the attackers quickly swapped and drained.

The stolen funds were funneled through privacy tools like Tornado Cash, making tracing tougher. Early signs pointed to a highly organized operation—no amateur script kiddies here.
How the Attack Worked: RPC Poisoning Made Simple
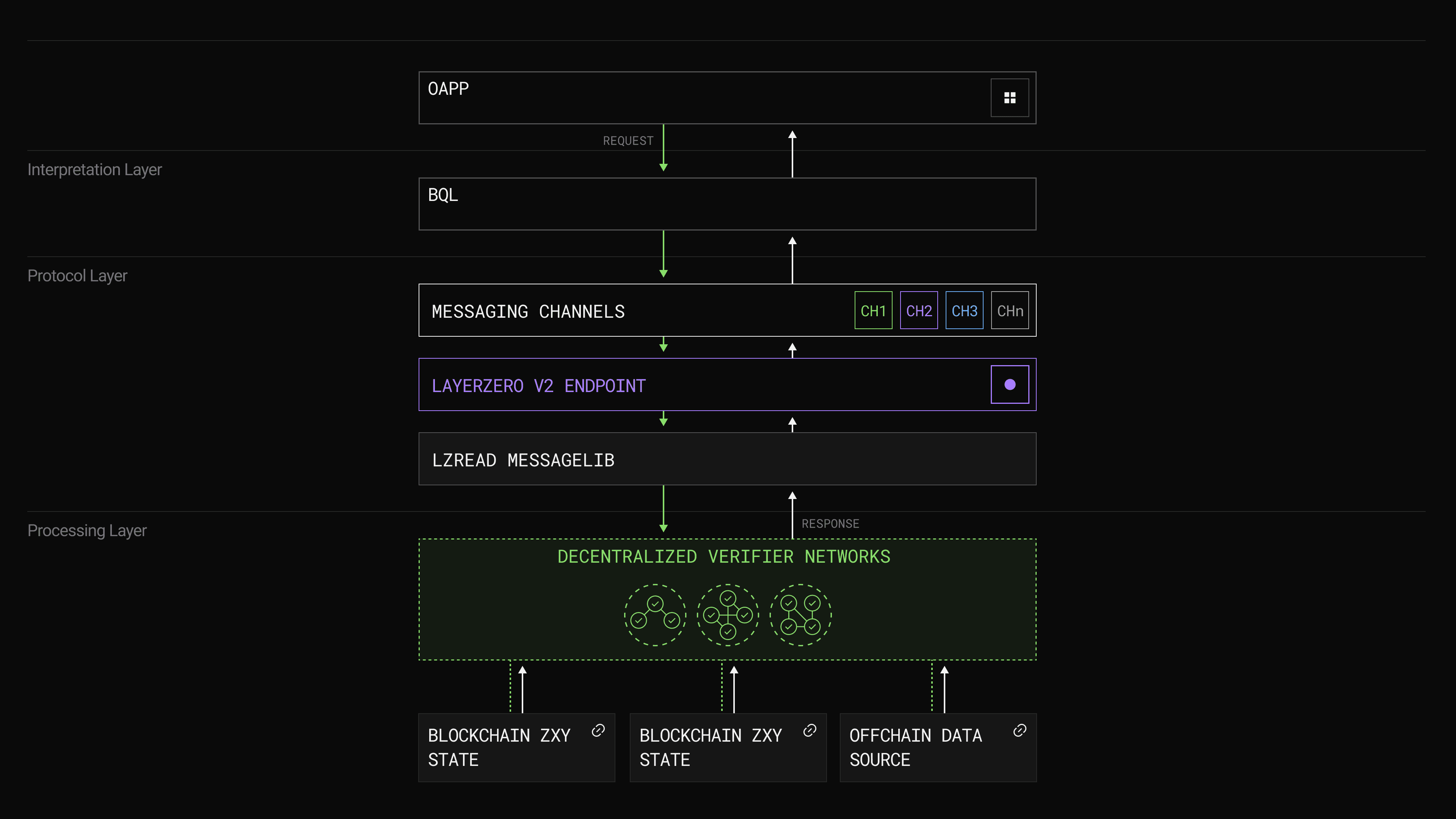
Think of cross-chain bridges like international airports for your crypto. LayerZero acts as the air traffic control, and DVNs (Decentralized Verifier Networks) are the independent inspectors double-checking every flight plan.
In this case:
- Attackers poisoned the data feeds feeding LayerZero’s DVN.
- A DDoS attack knocked out the legitimate servers.
- The single verifier accepted the forged message.
- Fake rsETH appeared on Ethereum, which attackers then used to borrow real assets on platforms like Aave.
No private keys were stolen from users, and the LayerZero protocol itself stayed intact. The breach was limited to KelpDAO’s specific setup.
LayerZero V2 Deep Dive. Everything you need to know about V2… | by Mark Murdock | LayerZero Official | Medium
LayerZero’s Response: “It Was the Single DVN Setup”
LayerZero was quick to publish a detailed incident statement. Their key point? KelpDAO ran a “1-of-1” DVN configuration—meaning only one verifier (LayerZero Labs’ own) was needed to approve messages. LayerZero says they had repeatedly urged partners to use multiple independent DVNs for redundancy, exactly to prevent this kind of single-point failure.
“This incident was isolated entirely to KelpDAO’s rsETH configuration as a direct consequence of their single-DVN setup,” the team emphasized. They also deprecated the compromised RPC nodes and brought the DVN back online safely.
In plain terms, it’s like having only one security guard watching the entire bank vault instead of a team cross-checking each other.
Understanding DVNs: The Unsung Heroes of Cross-Chain Security
DVNs are basically blockchain bodyguards. When you move tokens from one chain to another, a DVN verifies that the original transaction really happened before releasing funds on the destination side. LayerZero lets projects choose how many DVNs must agree—1-of-1 is the simplest (and riskiest) option, while multi-DVN setups require consensus from several independent verifiers.
The lzRead Deep Dive | LayerZero
LayerZero’s design gives projects full control over this security stack. The company argues this flexibility is a feature, but only if teams follow best practices for high-value assets.
The Blame Game: KelpDAO Pushes Back on LayerZero’s Narrative
Not everyone agrees with LayerZero’s version. KelpDAO has countered that the 1-of-1 setup was actually the default configuration in LayerZero’s own documentation and quick-start guides. They argue it wasn’t a reckless choice but the standard starting point many protocols used—claiming up to 40% of integrations followed the same pattern.
This back-and-forth highlights a common tension in DeFi: who’s responsible when defaults meet real-world scale?
Suspected Masterminds: North Korea’s Lazarus Group
LayerZero and on-chain analysts have preliminarily linked the attack to North Korea’s Lazarus Group (also known as TraderTraitor). This state-sponsored hacking collective has a long history of targeting crypto for funding—think massive heists used to support the regime’s programs.

The Lazarus heist: How North Korea almost pulled off a billion-dollar hack
If confirmed, this would mark another major Lazarus success in 2026, underscoring how nation-state actors are now treating DeFi bridges as high-yield targets.
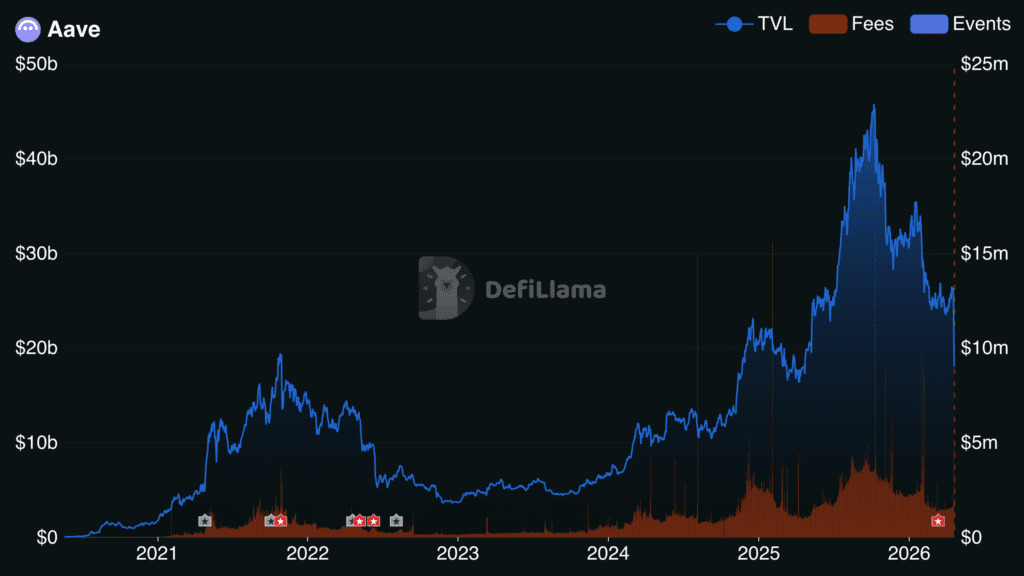
The Wider Impact: Aave Takes a Hit and DeFi TVL Drops
The ripple effects were immediate. Aave, one of the largest lending protocols, saw over $8 billion in TVL evaporate in days as markets reacted and rsETH-related positions turned into bad debt. DeFi’s overall locked value dipped sharply, with investors pulling funds amid fresh security fears.
Aave Loses $6B in TVL After KelpDAO rsETH Exploit | Our Crypto Talk
Several projects paused cross-chain activity as a precaution, showing how interconnected—and fragile—the ecosystem remains.
What This Means for You: Practical Lessons from the $290M Wake-Up Call
For everyday users staking, swapping, or bridging assets:
- Always check a project’s security configuration before trusting big money in it.
- Multi-verifier setups are now the gold standard for bridges handling hundreds of millions.
- Diversify across chains and protocols—don’t put all your eggs in one bridge basket.
For builders, the message is clear: defaults are convenient, but high TVL demands hardened security from day one.
The KelpDAO breach won’t be the last big hack, but it could be a turning point. As LayerZero and the industry double down on redundancy and transparency, users stand to benefit from safer cross-chain movement. In the fast-evolving world of DeFi, vigilance isn’t optional—it’s how the ecosystem matures. The real question now isn’t who was at fault, but how quickly everyone learns from it.






















